Foundations of Governance: Who Actually Owns Risk?
In our last post, we broke down the technical engine of Vulnerability Management (VM)—the 5-step lifecycle. But even the most sophisticated engine goes nowhere without a driver.
In the world of AppSec and AI development, technical teams often struggle to get traction. Scanners run, tickets pile up, and developers push back. The problem usually isn't the technology; it's the strategy. The difference between a reactive "whack-a-mole" program and a strategic operation is leadership.
While security teams handle scanning and assessment, leadership is responsible for ensuring VM aligns with business goals, risk priorities, and available resources. Without this alignment, VM becomes a fragmented, underfunded source of friction rather than a business enabler.
Here is how successful leaders shift VM from a "security problem" to a business priority.
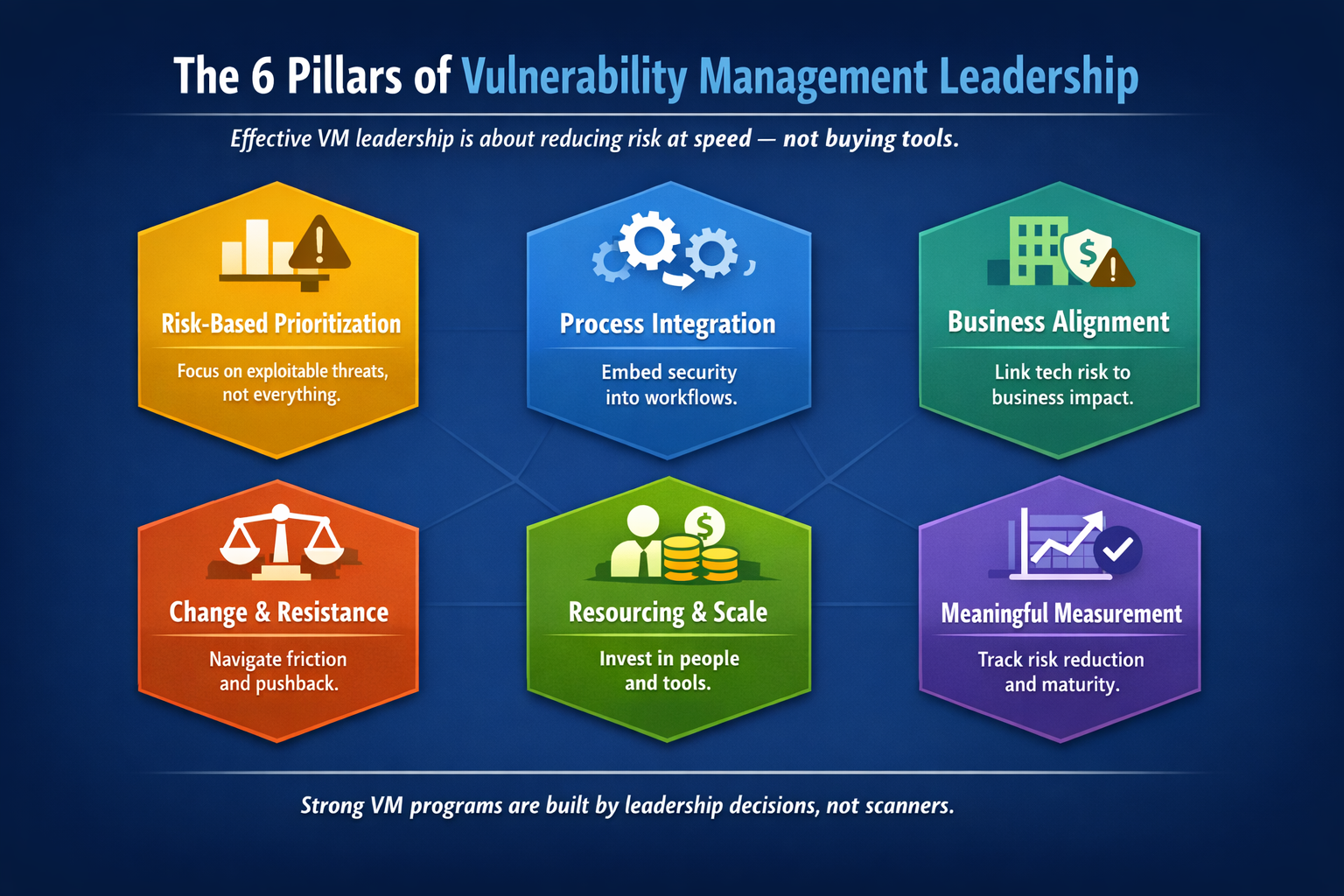
The Six Pillars of VM Leadership
Effective leadership goes beyond simply approving budget for a new tool. To build a program that survives in a high-speed DevOps environment, leaders must execute on six key responsibilities:
Drive Risk-Based Prioritization: You cannot fix everything. Leaders must authorize teams to focus on high-impact vulnerabilities (using data like EPSS) rather than chasing every theoretical bug.
Process Integration: VM cannot be a bolt-on. It must be embedded into existing IT and DevOps workflows (like CI/CD pipelines) to reduce friction.
Gain Business Buy-In: Technical risks must be translated into business impacts—financial loss, regulatory fines, or operational downtime—to capture executive attention.
Overcome Resistance: Pushback is inevitable. Strong leadership fosters a culture that navigates trade-offs between security and speed.
Secure Resources: A successful program needs people and funding. Leaders advocate for the budget required to scale.
Measure Success: Moving beyond "patch counts" to track metrics that demonstrate actual risk reduction and program maturity.
The Art of Translation: Speaking "Business" Not "CVSS"
A major hurdle for AppSec leaders is the language barrier. Business executives care about financial risk, uptime, and compliance—not CVSS scores or CVE IDs.
To gain buy-in, security leaders must bridge this gap by translating technical findings into business consequences. Instead of reporting "we have a critical vulnerability in the payment API," a strategic leader reports, "an unaddressed flaw in the payment system risks a 48-hour outage and regulatory non-compliance".
Why does this matter? When leadership understands the business impact, VM shifts from being viewed as a cost center to a competitive advantage. Organizations with robust security can demonstrate reliability to customers and partners, turning security into a market differentiator.
Overcoming the "Security vs. Innovation" Conflict
In dynamic environments like AI development, VM is often seen as a blocker. Resistance usually stems from a lack of resources or fear of disrupting production.
The solution is Shared Responsibility. Security cannot fix every vulnerability alone. Leaders must establish a governance model where:
Security identifies and analyzes the risk.
IT/DevOps owns the remediation.
Business Units own the accountability for the risk.
By embedding security discussions into regular business meetings and ensuring executives understand the impact of inaction, leaders can break down silos and foster a culture where security is everyone's job.
The Bottom Line
Tools find vulnerabilities; people and processes fix them. If your VM program is stalling, stop looking for a better scanner and start looking at your strategy. By aligning security efforts with business goals and translating risk into financial terms, you can transform VM from a technical checklist into a critical layer of business resilience.