Foundations of Exposure: How the VM Lifecycle Applies to AppSec & AI
If you think Vulnerability Management (VM) is just about running a scanner once a month and applying patches, it is time for a strategy update.
In the fast-paced world of cybersecurity, treating VM as a checklist task is a recipe for disaster. True VM is a structured, risk-reduction process designed to minimize exposure across the organization. Rather than just finding technical glitches, it is about continuously identifying weaknesses, understanding which ones pose a real threat, and acting based on actual risk.
Why must it be continuous? Industry frameworks define VM as a continuous lifecycle rather than a one-time event. Because software changes, configurations drift, and new threats emerge daily, a "point-in-time" scan is instantly outdated. Treating VM as an ongoing process is the only way to catch exposures introduced by new software, misconfigurations, or zero-day threats.
The Bridge: Adapting the Cycle for AI & AppSec
While the core phases of Vulnerability Management remain constant, the implementation looks very different for developers building AI-driven applications.
In traditional IT, an asset is a server, and a fix is usually a patch. In the world of AppSec and AI, an "asset" might be a large language model (LLM), an API endpoint, or a piece of immutable smart contract code. Here, remediation isn't always about updating software; it often involves implementing runtime guardrails to prevent prompt injection or "shifting left" to fix Infrastructure as Code (IaC) templates before deployment,. The lifecycle is the same, but the tactics must evolve to match the speed and complexity of modern development.
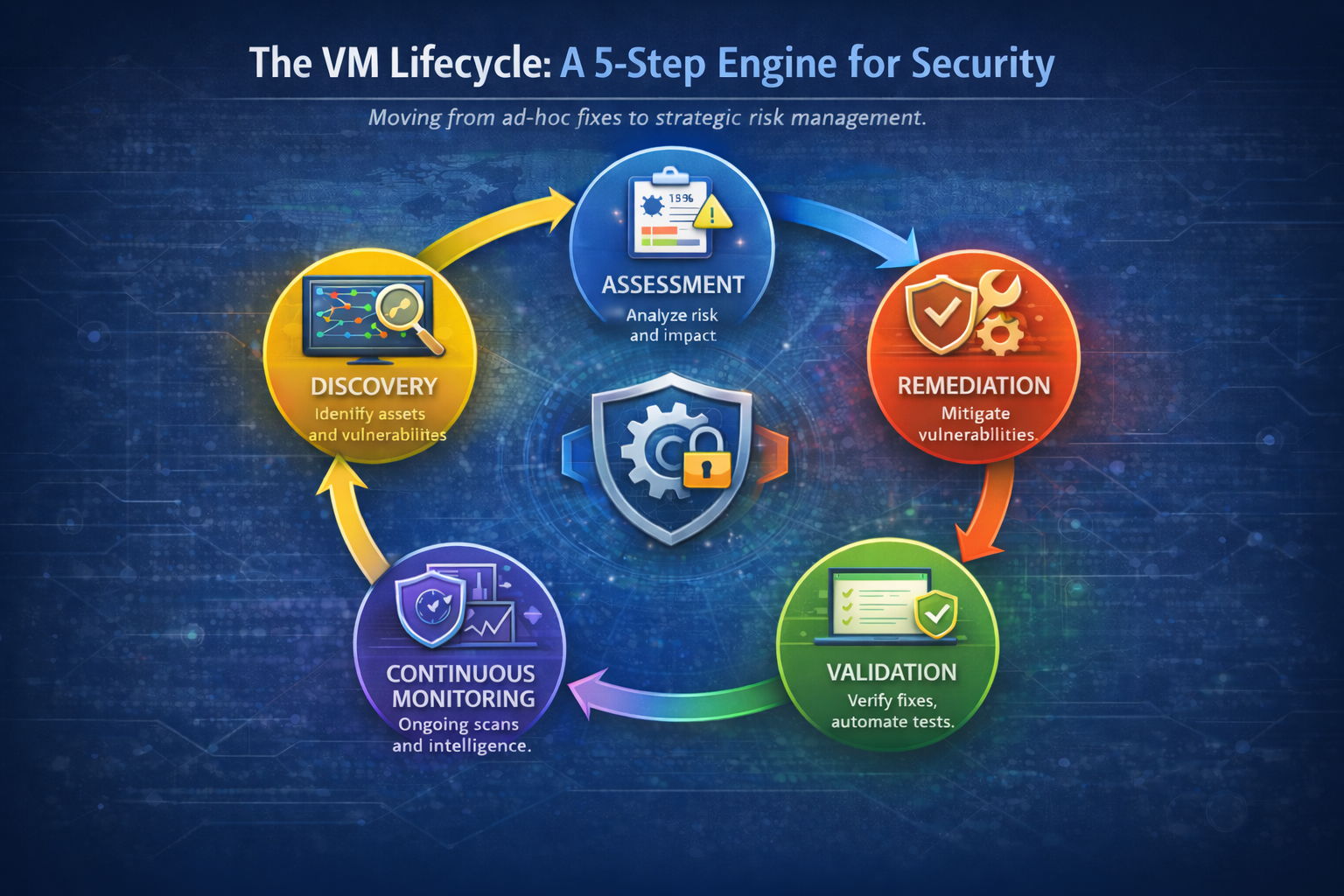
The VM Lifecycle: A 5-Step Engine for Security
To move from ad-hoc fixes to strategic risk management, organizations follow a structured lifecycle. Here is how that blueprint applies to securing your code and models:
Discovery: You cannot protect what you do not know. This phase identifies assets and their associated vulnerabilities to create an accurate inventory. For AI, this means discovering "unseen assets" like shadow AI models, third-party libraries, and API dependencies that traditional scanners often miss.
Assessment: Once identified, vulnerabilities are analyzed to understand their severity and potential impact. In AppSec, this means looking beyond generic CVSS scores to understand reachability—is this vulnerable library actually loaded by the application? It also involves using context like CISA’s Known Exploited Vulnerabilities (KEV) and EPSS to separate theoretical risks from real threats.
Remediation: This is the action phase involving prioritization and fixes. Since you cannot always "patch" a machine learning model without retraining it, remediation often relies on compensating controls—like input filtering or network segmentation—to mitigate the risk without breaking the application.
Validation: Trust, but verify. This step assures that remediation efforts were successful. In modern development, this requires automated validation (like Breach and Attack Simulation) to ensure a bad configuration doesn't make it to production.
Continuous Monitoring: Because the threat landscape evolves, regular scanning and threat intelligence integration are required. For AI systems, this means monitoring for behavioral drift and logic abuse, not just static software bugs.
Context is King: One Size Does Not Fit All
A critical mistake in VM is trying to apply the exact same process to every part of the business. The VM lifecycle must be tailored to the specific environment it protects.
While the core steps (Discovery through Monitoring) remain the same, the implementation changes drastically depending on the technology stack:
Traditional IT Infrastructure: Focuses on OS and software patching, keeping workstations and servers compliant with security policies.
Cloud Environments: Deals with dynamic assets that may live for seconds, shared responsibility models, and misconfigurations rather than just software flaws.
Application Development: Shifts focus to code security, integrating checks into CI/CD pipelines, and managing dependencies (SCA).
Operational Technology (OT): Prioritizes uptime and legacy system stability. You often cannot patch a medical device or a factory controller as frequently as a laptop, so network segmentation and compensating controls become key.
The Bottom Line
Vulnerability Management is not just a technical task—it is a critical business function. By moving away from a checklist mentality and embracing a continuous, risk-based lifecycle, developers and security leaders can stop chasing every bug and start reducing the risks that actually threaten the business.